CronSearch www.iotworldtoday.com: Successful IoT Use Cases Require a Solid Strategy You don’t necessarily need cutting-edge AI or 5G to be successful with an IoT project. ... www.iotworldtoday.com: Smart Building Sensors for Schools and Vaping ...

CronSearch www.iotworldtoday.com: Successful IoT Use Cases Require a Solid Strategy You don’t necessarily need cutting-edge AI or 5G to be successful with an IoT project. ... www.iotworldtoday.com: Smart Building Sensors for Schools and Vaping ...
CronSearch www.iotworldtoday.com: Successful IoT Use Cases Require a Solid Strategy You don’t necessarily need cutting-edge AI or 5G to be successful with an IoT project. ... www.iotworldtoday.com: Smart Building Sensors for Schools and Vaping ...

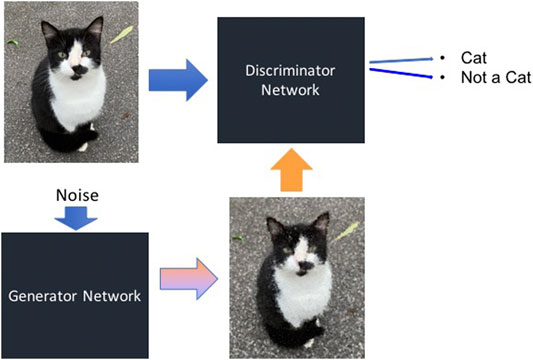
Future Internet | Free Full-Text | iCaps-Dfake: An Integrated Capsule-Based Model for Deepfake Image and Video Detection | HTML